Aperio Basics: Interpreting Results
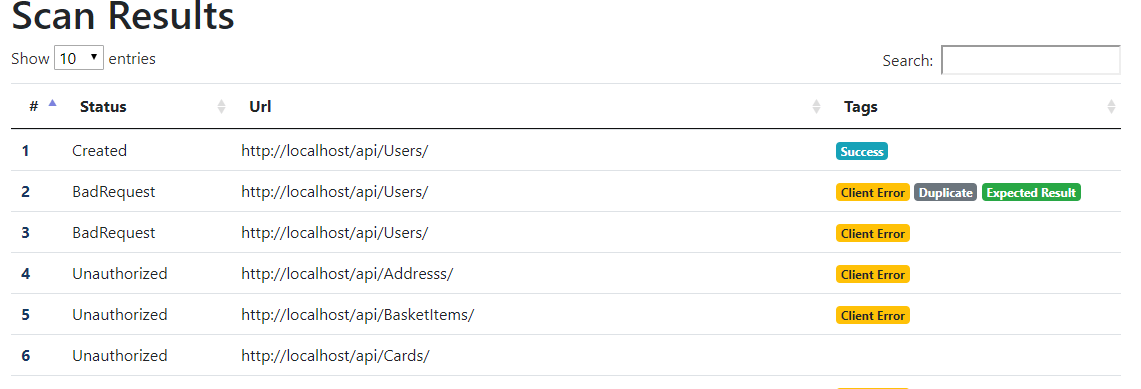
Within each run, you should see each unique behavior produced by the fuzzer. By clicking on a behavior, you can see the sequence of requests that produced that result:
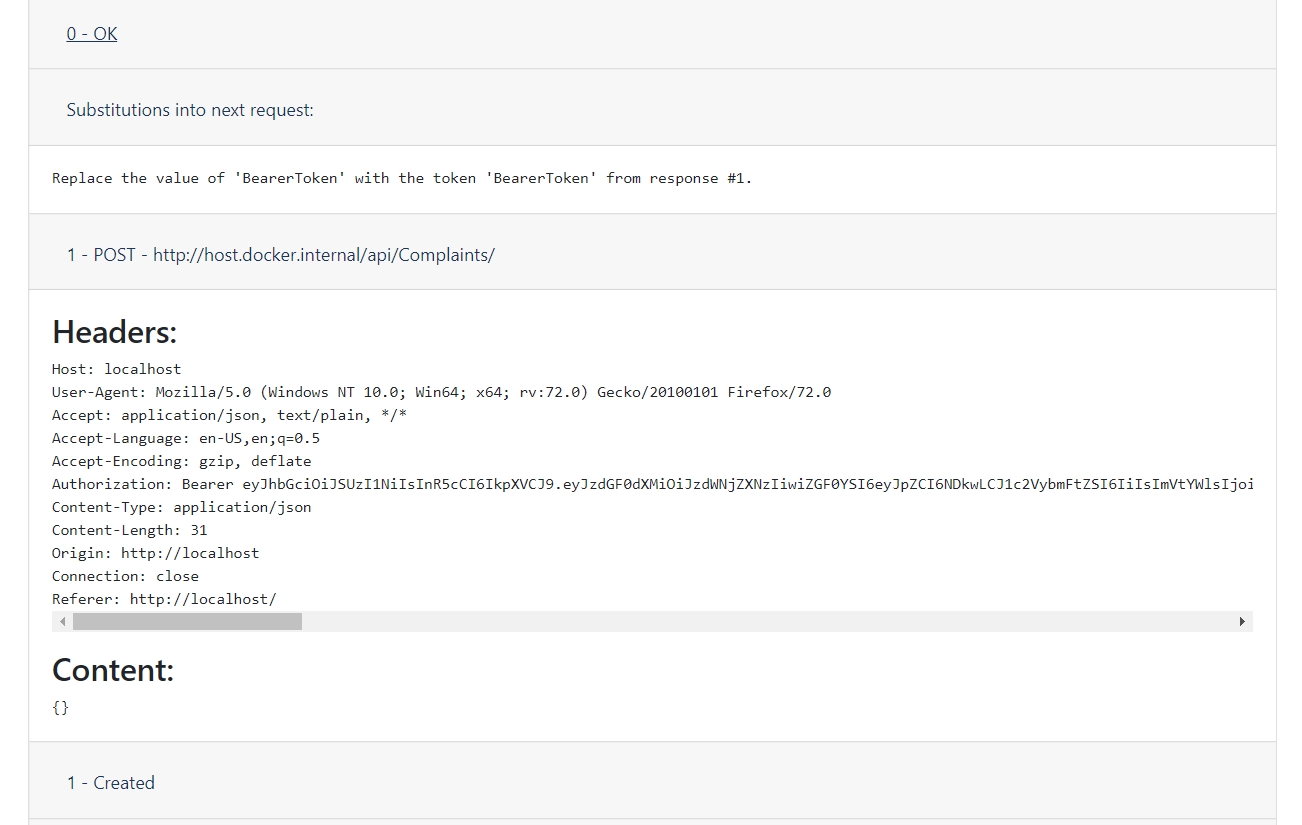
Requests start out with a tag indicating the HTTP status of the final response, which helps to highlight things like server errors. You can add additional tags to indicate duplicates and potential bugs.
This is the end of the tutorial, for now. If you have any feedback or just want to know more about how the fuzzer works, I’d love to hear from you at max@aperiosecurity.com. Happy hacking!
